Advertisement
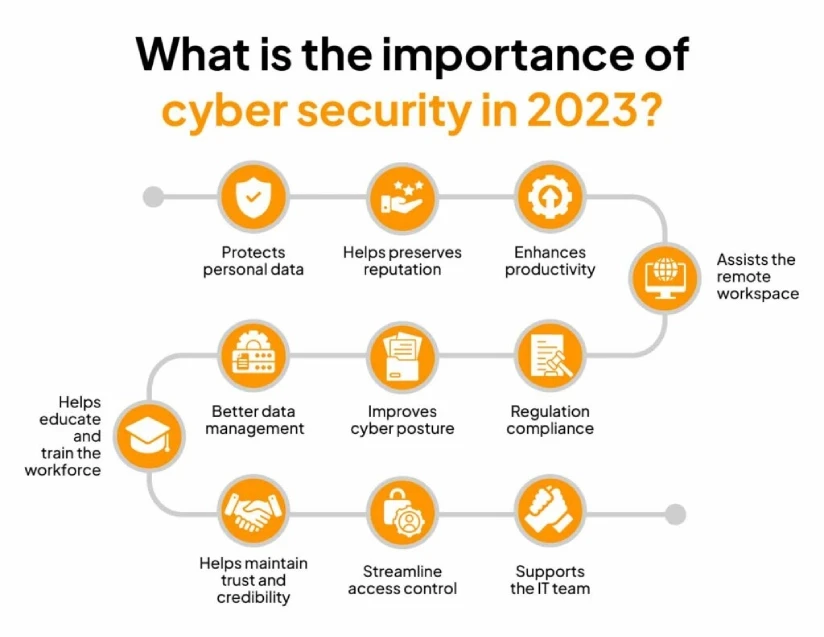
CRM Software – Cybersecurity is indispensable for protecting sensitive information, ensuring uninterrupted business operations, and mitigating financial losses from cyber threats. As cyberattacks escalate in complexity and frequency, organizations across sectors—especially healthcare and critical infrastructure—must adopt comprehensive cybersecurity measures that integrate technical defenses with strategic governance. The evolving threat landscape underscores the necessity of cybersecurity as a core enterprise risk management function, extending beyond IT departments to involve business leaders, regulators, and supply chain partners.
Cyber threats jeopardize personal, corporate, and patient data integrity, exposing organizations to unauthorized access, ransomware, and operational disruptions. According to IBM’s Cost of a Data Breach Report 2024, the average cost of a data breach has surged to $4.35 million, highlighting the immense financial stakes. Healthcare institutions face additional pressure, as cybersecurity lapses can directly impact patient safety and regulatory compliance. Prominent cyber incidents, such as the MOVEit ransomware attack, illustrate the global and multifaceted nature of cyber risks, affecting cloud services, third-party vendors, and business continuity. This article delves into why cybersecurity is critical, examines sector-specific implications, explores evolving threats, and outlines strategic frameworks and technologies that empower organizations to build cyber resilience.
Core Reasons Cybersecurity Is Critical
Cybersecurity’s primary function is safeguarding sensitive data from unauthorized access and exploitation. This encompasses personal identifiable information (PII), intellectual property, financial records, and in healthcare, protected health information (PHI). Data breaches compromise confidentiality, enabling identity theft, fraud, and regulatory penalties. The increasing reliance on digital infrastructures and cloud services such as Amazon Web Services (AWS) expands the attack surface, demanding robust encryption, access controls, and continuous monitoring.
Advertisement
Beyond data protection, cybersecurity ensures business continuity by preventing operational disruptions caused by cyber incidents. Ransomware gangs like CL0P deploy sophisticated malware that can encrypt critical files, halting production lines or healthcare delivery. The ability to maintain uptime during and after attacks is essential for preserving revenue streams and customer trust. Cybersecurity also mitigates reputational damage, which can have long-term effects on market positioning.
Regulatory compliance is another critical driver, with laws such as HIPAA in healthcare, GDPR in Europe, and various U.S. state data privacy regulations mandating stringent security measures. Non-compliance can result in hefty fines and legal actions, amplifying the financial impact of cyber incidents. Organizations must embed cybersecurity within governance frameworks to align with these requirements and demonstrate due diligence.
Cybersecurity in Healthcare: A Case Study in Patient Safety
Healthcare organizations are prime targets for cyberattacks due to the sensitivity of patient data and the critical nature of healthcare services. Cyber threats in this sector include ransomware, data theft, and disruptions to medical devices or hospital systems. The American Hospital Association (AHA) emphasizes cybersecurity as a patient safety priority, recognizing that breaches can delay care, lead to diagnostic errors, or compromise treatment plans.
Expert insights from FBI veteran John Riggi underscore cybersecurity’s role in enterprise risk management within healthcare. He advocates for integrating cybersecurity risk assessments into overall hospital governance to prioritize investments and response planning effectively. The MOVEit ransomware attack, which exploited vulnerabilities in managed file transfer software, exemplifies how third-party software risks can cascade into patient safety hazards by interrupting critical data flows.
Healthcare’s complex supply chains and vendor relationships further complicate cybersecurity. Third-party risk assessments are essential to identify vulnerabilities in cloud platforms, medical device manufacturers, and service providers. SentinelOne and UpGuard stress that continuous monitoring and risk prioritization frameworks improve resilience against evolving threats and regulatory scrutiny.
The Evolving Cyber Threat Landscape
cyber threats are increasingly sophisticated, leveraging social engineering, ransomware, phishing, and cloud misconfigurations. Ransomware gangs like CL0P have evolved tactics to include double extortion, where attackers threaten to release stolen data publicly if ransom demands are unmet. These attacks exploit software vulnerabilities and human factors, making comprehensive cybersecurity training and patch management indispensable.
Phishing remains a prevalent vector, with attackers using targeted emails to gain initial access. The rise of cloud computing introduces risks related to misconfigured storage buckets, inadequate identity management, and insecure APIs, which adversaries exploit to bypass traditional defenses. For instance, the MOVEit breach demonstrated how attackers exploited software vulnerabilities to access sensitive data across multiple organizations, causing widespread operational disruption.
The growing adoption of remote work and digital transformation has expanded the attack surface, challenging organizations to secure endpoints, networks, and cloud environments cohesively. Cybercriminals capitalize on these expanded vectors, necessitating multi-layered defense strategies and real-time threat intelligence.
Strategic Cybersecurity Management for Business Leaders
Cybersecurity is no longer solely a technical issue but a strategic business imperative requiring boardroom involvement. Business leaders must embrace cybersecurity as a component of enterprise risk management, integrating it into governance, compliance, and operational continuity planning. This shift is critical to ensure adequate resource allocation and organizational accountability.
Risk prioritization frameworks help leaders focus on the most critical vulnerabilities that could cause significant financial or operational harm. Accenture highlights that organizations with mature vulnerability management reduce breach likelihood and impact. Third-party risk assessments also safeguard supply chains by identifying and mitigating risks from vendors, service providers, and cloud platforms.
Leadership engagement fosters a security culture that permeates the organization, supporting policies, training, and incident response readiness. Effective communication between cybersecurity teams and executives ensures alignment with business objectives and regulatory mandates, enhancing overall security posture.
Financial and Operational Implications of Cybersecurity Failures
The financial toll of cybersecurity failures is substantial and rising. IBM’s 2024 report indicates an average breach cost of $4.35 million, factoring in detection, response, legal fees, customer churn, and fines. Industries such as healthcare experience even higher costs due to regulatory penalties and patient safety risks.
Operational disruptions from cyberattacks extend beyond immediate downtime. Prolonged recovery periods can erode customer confidence, damage brand reputation, and reduce market competitiveness. For healthcare providers, interruptions can delay critical treatments and compromise care quality, potentially leading to life-threatening outcomes.
Investing in cybersecurity supports business continuity by minimizing downtime and data loss. Organizations that embed cybersecurity into their continuity plans recover faster, maintain regulatory compliance, and protect shareholder value.
Technologies and Best Practices in Cybersecurity
Comprehensive cybersecurity strategies encompass endpoint protection, encryption, identity and access management (IAM), and cloud security controls. Endpoint protection platforms such as SentinelOne utilize AI and machine learning to detect and respond to threats in real time, reducing dwell time and damage.
Encryption safeguards data at rest and in transit, ensuring confidentiality even if breaches occur. Cloud security requires continuous configuration management, identity federation, and monitoring to prevent misconfigurations that attackers exploit.
Governance integration is essential, embedding cybersecurity into business continuity, incident response, and compliance frameworks. Automation and AI-driven threat detection improve response agility and reduce human error. Organizations must also emphasize continuous employee training to counter social engineering tactics.
Forward-Looking Cybersecurity Imperatives
As cyber threats evolve, organizations must adopt dynamic cybersecurity strategies that combine technological innovation with strategic governance. Increasing regulatory complexity demands proactive compliance and risk management. Business leaders should champion cybersecurity investments that enhance resilience, protect sensitive data, and support operational stability.
Emerging technologies such as AI-powered analytics and zero-trust architectures will play pivotal roles in future defenses. Continuous improvement through threat intelligence sharing, red teaming, and supply chain risk management will enhance cyber resilience. Integrating cybersecurity into organizational culture and enterprise risk frameworks ensures preparedness against increasingly sophisticated adversaries.
The imperative for cybersecurity investment is clear: it safeguards trust, preserves business continuity, and protects the most valuable asset—information.
FAQ
Why is cybersecurity important for businesses?
Cybersecurity protects businesses from unauthorized access to sensitive data, prevents operational disruptions caused by cyberattacks, reduces financial losses from breaches, and ensures compliance with data privacy regulations. It supports business continuity and safeguards reputation, which are critical for sustaining competitive advantage.
How does cybersecurity impact patient safety in healthcare?
In healthcare, cybersecurity protects patient data and ensures the integrity of medical systems. Cyberattacks can delay treatments, corrupt health records, or disable medical devices, directly endangering patient safety. Embedding cybersecurity into healthcare governance prioritizes patient safety as part of enterprise risk management.
What are common cyber threats organizations face today?
Organizations face ransomware attacks, phishing scams, social engineering, cloud misconfigurations, and supply chain vulnerabilities. Attackers increasingly use sophisticated tactics like double extortion ransomware and exploit human factors alongside technical weaknesses.
How can business leaders effectively manage cyber risk?
Leaders should integrate cybersecurity into enterprise risk management, prioritize vulnerabilities based on business impact, conduct third-party risk assessments, and foster a security-aware culture. Aligning cybersecurity strategies with business objectives and compliance requirements enhances organizational resilience.
What technologies are essential for modern cybersecurity defenses?
Essential technologies include endpoint detection and response (EDR), AI-driven threat analytics, encryption, identity and access management (IAM), and cloud security platforms. Automation and continuous monitoring enable rapid detection and response to emerging threats.
For further expert insights on cybersecurity’s importance in healthcare, visit the American Hospital Association’s cybersecurity resource. For foundational cybersecurity concepts and best practices, see SentinelOne’s cybersecurity overview.
Advertisement