Advertisement
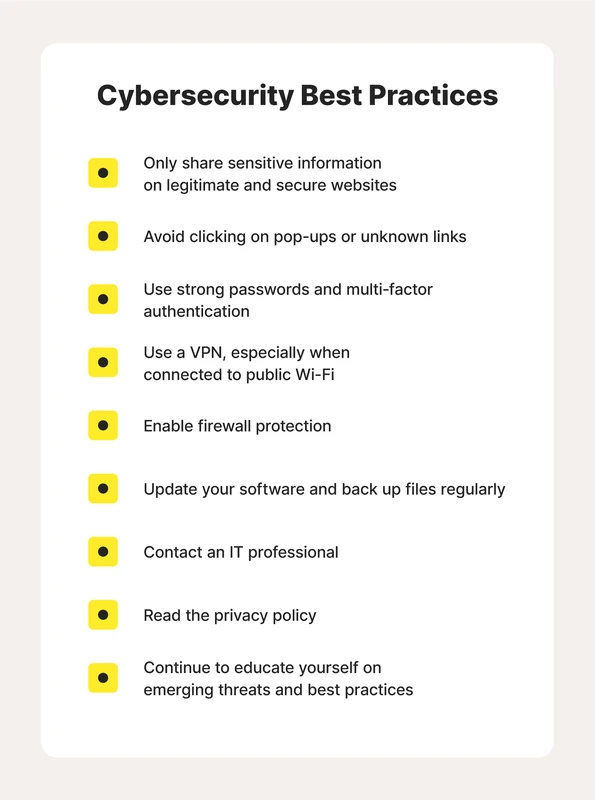
CRM Software – Cybersecurity fundamentals are critical for protecting devices, data, and networks against an expanding array of cyber threats that target individuals, businesses, and government entities alike. Effective cybersecurity involves multiple layers of defenses, including strong password practices, multi-factor authentication (MFA), regular software updates, data encryption, secure backup systems, and user education. These measures together help mitigate risks posed by malware, phishing attacks, ransomware, and insider threats, which continue to evolve in sophistication and frequency. Understanding the foundational principles of cybersecurity, such as the CIA triad (Confidentiality, Integrity, Availability), is essential for anyone looking to strengthen their digital security posture.
Cyberattacks frequently exploit vulnerabilities in systems that lack robust security controls, making it imperative to implement comprehensive protective strategies. Small businesses, often targeted due to limited resources, must prioritize cybersecurity basics, including operational security and incident response planning, to reduce exposure. Likewise, government agencies and IT security professionals emphasize proactive measures like network security and ethical hacking to identify weaknesses before attackers do. By integrating password managers, firewalls, encryption, and continuous user training, organizations and individuals can build resilient defenses that align with industry best practices and compliance requirements.
Core Principles: The CIA Triad in Cybersecurity
The CIA triad—Confidentiality, Integrity, and Availability—forms the bedrock of cybersecurity principles guiding the protection of information assets. Confidentiality ensures that sensitive data remains accessible only to authorized users, preventing unauthorized disclosure. Techniques such as data encryption, access controls, and secure communication protocols uphold this principle, especially critical in sectors handling personal or financial information.
Advertisement
Integrity guarantees that data remains accurate, complete, and unaltered during storage, transmission, or processing. Mechanisms like checksums, digital signatures, and hashing algorithms detect unauthorized modifications, ensuring trustworthiness. For example, a healthcare provider must maintain data integrity to avoid misdiagnosis caused by tampered records.
Availability focuses on ensuring reliable and timely access to data and systems when needed. Denial-of-Service (DoS) attacks, hardware failures, or software bugs threaten this availability, which can be mitigated through redundant systems, failover strategies, and robust backup solutions. Maintaining availability is vital for critical infrastructure and e-commerce platforms where downtime incurs significant costs.
Together, these principles guide cybersecurity strategies, balancing protection against unauthorized access, data accuracy, and system accessibility to create a secure digital environment.
Essential Protective Measures Against Cyber Threats
Strong password practices remain foundational in defending against unauthorized access. Complex passwords combining uppercase and lowercase letters, numbers, and symbols reduce susceptibility to brute force attacks. However, managing numerous complex passwords is challenging for users, making password managers indispensable tools. These applications generate, store, and autofill secure passwords, minimizing reuse and weak credentials.
Multi-factor authentication (MFA) adds a critical layer by requiring users to verify identity through multiple forms, such as a password plus a biometric scan or a one-time code sent to a mobile device. Studies show MFA can block up to 99.9% of automated cyberattacks, significantly enhancing account security beyond passwords alone.
Keeping software and security systems updated addresses vulnerabilities that cybercriminals exploit. Patch management processes ensure timely application of security updates to operating systems, applications, and firmware. For instance, ransomware often targets unpatched systems, underscoring the need for automated updates and vulnerability scanning tools.
Firewalls and antivirus software provide frontline defenses by monitoring incoming and outgoing network traffic and detecting malicious software. Modern firewalls incorporate deep packet inspection and intrusion prevention systems (IPS), while antivirus solutions use heuristic analysis and machine learning to identify new and evolving malware threats. Regularly updating these tools is essential to maintain effectiveness against the latest attack vectors.
Data Security and Backup Strategies
Encrypting sensitive data both at rest and in transit safeguards information from interception and unauthorized access. Advanced encryption standards (AES) with 256-bit keys are widely adopted for data storage, while Transport Layer Security (TLS) protocols secure data moving across networks. This dual approach protects everything from stored customer records to email communications.
Regular data backups are indispensable for recovery from cyber incidents such as ransomware attacks or accidental deletions. Combining offline backups (physically disconnected storage), cloud backups, and external storage devices ensures redundancy and resilience. The 3-2-1 backup rule—three copies of data, stored on two different media types, with one offsite—remains a best practice to mitigate data loss.
Secure disposal of electronic files and devices prevents data leakage when decommissioning hardware or deleting sensitive information. Techniques such as data wiping, degaussing, and physical destruction of storage media are employed depending on the sensitivity of the data and regulatory requirements. Organizations must adopt clear policies and procedures for data disposal to avoid potential breaches.
Network and Application Security
Protecting networks against intrusions requires layered defenses including segmented networks, secure configurations, and continuous monitoring. network security tools such as intrusion detection systems (IDS) and intrusion prevention systems (IPS) analyze traffic patterns to identify suspicious activities and block potential threats. Virtual private networks (VPNs) encrypt remote connections, vital for secure telework environments.
Application security spans the entire software development lifecycle, incorporating secure coding practices, regular vulnerability assessments, and penetration testing. Early integration of security controls reduces risks of exploits like SQL injection or cross-site scripting (XSS). Operational security complements this by enforcing strict access controls, monitoring user activities, and managing system configurations to prevent insider threats and unauthorized changes.
User Training and Cyber Hygiene
Human factors often represent the weakest link in cybersecurity. Educating employees and users on recognizing phishing attempts, social engineering tactics, and suspicious email characteristics is essential. Training programs tailored to organizational roles enhance awareness and preparedness, reducing the likelihood of successful attacks.
Safe browsing habits and cautious handling of sensitive information further strengthen cyber hygiene. This includes verifying website authenticity, avoiding unsecured public Wi-Fi for confidential activities, and using secure disposal methods for electronic files. Regular simulated phishing exercises help maintain vigilance and measure training effectiveness.
Developing and Implementing Cybersecurity Policies
Comprehensive cybersecurity policies establish clear guidelines for access control, acceptable use, and incident response. Access control policies define user permissions based on roles and the principle of least privilege, limiting exposure. Usage policies address appropriate handling of devices, software, and data to reduce risk.
Incident response plans outline steps for detecting, containing, and recovering from security incidents. These plans integrate communication protocols, roles, and responsibilities to minimize damage and downtime. Regular testing of response plans through drills ensures organizational readiness.
Risk management frameworks assess potential threats and vulnerabilities, prioritizing mitigation efforts aligned with organizational goals and compliance mandates. For example, small businesses might follow frameworks recommended by the FTC or CISA to develop tailored cybersecurity strategies that optimize resource allocation.
Emerging Trends and Advanced Concepts
Ethical hacking and penetration testing serve as proactive measures to identify security gaps before adversaries exploit them. Certified professionals simulate attacks to evaluate defenses, providing actionable insights to improve security posture.
Cloud security fundamentals have become critical as organizations migrate infrastructure to cloud platforms. Securing cloud environments involves shared responsibility models, encryption, identity and access management (IAM), and continuous monitoring to protect data and applications.
Advancements in identity and access management leverage biometrics, artificial intelligence, and behavioral analytics to enhance authentication and detect anomalies. These technologies improve both security and user experience by adapting to evolving threat landscapes.
Cybersecurity Measure |
Purpose |
Example Tools/Methods |
Effectiveness |
|---|---|---|---|
Strong Passwords & Managers |
Prevent unauthorized access |
LastPass, Bitwarden, complex passphrases |
Reduces password-related breaches by 80% |
Multi-Factor Authentication (MFA) |
Additional verification layer |
Authenticator apps, SMS codes, biometrics |
Blocks ~99.9% of automated attacks |
Software Updates & Patch Management |
Close vulnerabilities |
Windows Update, automatic patches |
Essential for preventing exploits |
Firewalls & Antivirus |
Monitor and block threats |
Cisco ASA, Norton Antivirus |
Detects and mitigates malware |
Data Encryption |
Protect data confidentiality |
AES-256, TLS |
Secures data at rest and in transit |
Regular Backups |
Ensure data availability & recovery |
Cloud backup services, external drives |
Mitigates ransomware and data loss |
FAQ
What are the most common types of cyberattacks?
Common cyberattacks include malware infections, phishing scams, ransomware attacks, denial-of-service (DoS) attacks, and insider threats. Each exploits specific vulnerabilities, from tricking users into clicking malicious links to overwhelming network resources.
How does multi-factor authentication improve security?
Multi-factor authentication requires users to provide two or more verification factors, making unauthorized access significantly more difficult even if passwords are compromised. This layered defense effectively blocks nearly all automated cyberattacks.
Why is regular software updating critical for cybersecurity?
Software updates patch security vulnerabilities that attackers exploit. Delayed or missing updates leave systems exposed to known threats, increasing the risk of breaches and malware infections.
How can small businesses implement effective cybersecurity with limited resources?
Small businesses should focus on basic measures like strong passwords, enabling MFA, maintaining updated software, training employees on cyber hygiene, and establishing simple incident response plans. Leveraging free or affordable tools and guidance from agencies like the FTC and CISA can optimize security efforts.
What role does user training play in preventing cyber threats?
User training raises awareness about phishing, social engineering, and safe computing practices, reducing human errors that often enable attacks. Educated users act as a critical first line of defense by recognizing and reporting suspicious activities.
Cybersecurity basics continue to evolve with emerging threats and technologies. Staying informed about advanced defenses such as ethical hacking, cloud security, and identity management will be essential for future resilience. Organizations and individuals should regularly assess their security posture, update policies, and invest in ongoing training to adapt to the dynamic cyber landscape.
For more detailed guidance on cybersecurity best practices, consult authoritative resources like the FTC’s cybersecurity factsheets for small businesses and the Cybersecurity and Infrastructure Security Agency’s best practices.
Advertisement